Zscaler for OTはOT環境をサイバー脅威から保護することで、工場の稼働時間を増やしながら、従業員や工場の安全性を改善し、新しいビジネス モデルを実現します。
これまで以上に脆弱な現代の工場
サイバー攻撃は予定外の稼働停止時間を引き起こすだけでなく、従業員や工場を危険にさらします。プラントなどの大規模施設や工場がさまざまなシステムとつながるようになったことで、運用に関するサイバーフィジカル リスクを考慮する必要性が高まっています。

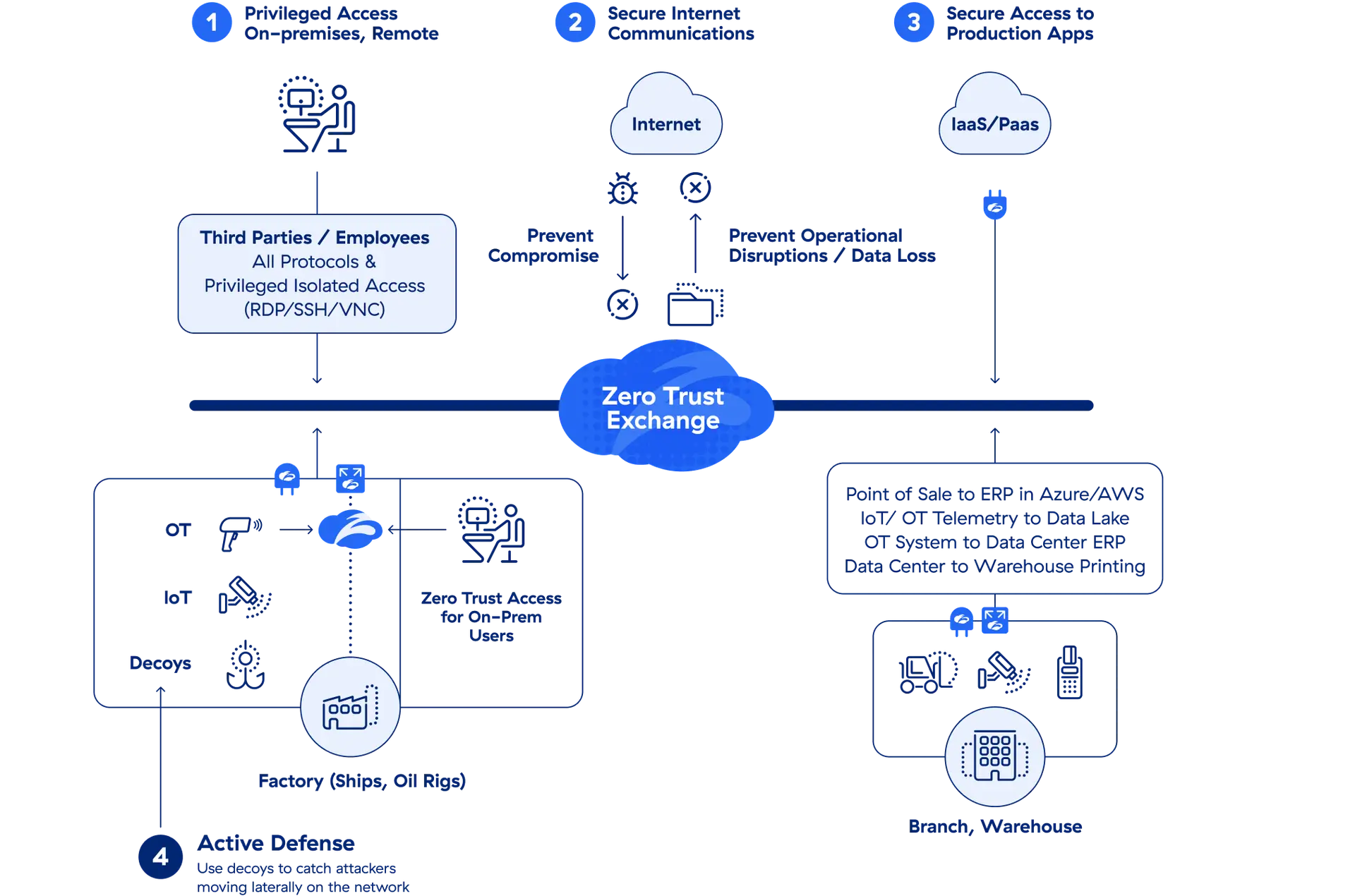
サードパーティーと従業員に完全に分離された接続を提供することで、予知保全を目的とした装置への高速アクセスが実現し、稼働停止時間を最小限に抑えられます。
OTネットワークやOTシステムはインターネットから見えないため、攻撃者が生産ラインを妨害することはできません。
リモート ワーカーやサードパーティー ベンダーは、従来のVPNの煩わしさを感じることなくOTシステムにアクセスできるようになります。

詳細
ゼロトラストでOTとIoTシステムを保護
あらゆる課題を解消するために構築されたソリューション

完全に隔離されたRDP、SSHセッションを用いたクライアント不要のリモート アクセスを通じ、サードパーティー ベンダーとリモート ユーザーがどこからでも装置に接続できる環境を整えます。


IIoT、ICS、SCADAシステムがインターネットを介して、運用および保守のデータをパブリック クラウド アプリケーションと安全に共有できるようにします。


従業員やデバイスに対し、生産現場からOT生産システムへの高速な直接アクセスを提供することで、予知保全を容易にします。


拠点と管理倉庫のOTやIoTデバイスを、パブリックまたはプライベート クラウド上のアプリケーションに安全に接続します。


重要なインフラストラクチャーへの侵入を試みるアクティブな攻撃者を検出して封じ込め、生産ラインを保護します。



Zscalerでネットワークとアプリを変革したMAN Energy Solutions
Zscaler Zero Trust Exchangeの特長
ポイント製品を排除して運用のオーバーヘッドを削減する包括的なクラウド プラットフォーム
01 サイバー脅威対策
ユーザー、ワークロード、デバイスを保護する総合的なアプローチ
02 データ保護
SSEプラットフォーム全体にわたる完全なデータ保護のためのフルTLS/SSLインスペクション
03 ゼロトラスト接続
ネットワークではなくアプリに接続させることで、ラテラル ムーブメントを防止するZTNA
04 デジタル エクスペリエンス管理
パフォーマンスの問題を特定して修正

デモを依頼
ZscalerがOTの保護にどのように役立つのかをご紹介します。今すぐデモをご予約ください。











