In April 2022, Adobe released security update APSB22-16. This update fixed five product bugs that Zscaler’s ThreatLabz reported in Adobe Acrobat that are related to EMF (Enhanced Metafile Format) parsing. Adobe determined that Acrobat is secure by default for converting EMF to PDF. Specifically, abuse requires administrative privileges to modify the registry and add HKLM keys in order to enable the feature of the conversion from EMF to PDF. As a result, Adobe treated these five issues as regular product bugs instead of security bugs. Nevertheless, in this blog, we will present details related to these discoveries.
Known Affected Software
- Acrobat DC 22.001.20085 and earlier versions
- Acrobat 2020 20.005.30314 and earlier versions (Windows) 20.005.30311 and earlier versions (macOS)
- Acrobat 2017 17.012.30205 and earlier versions
Steps to Reproduce
- Enable Page Heap in Acrobat.exe
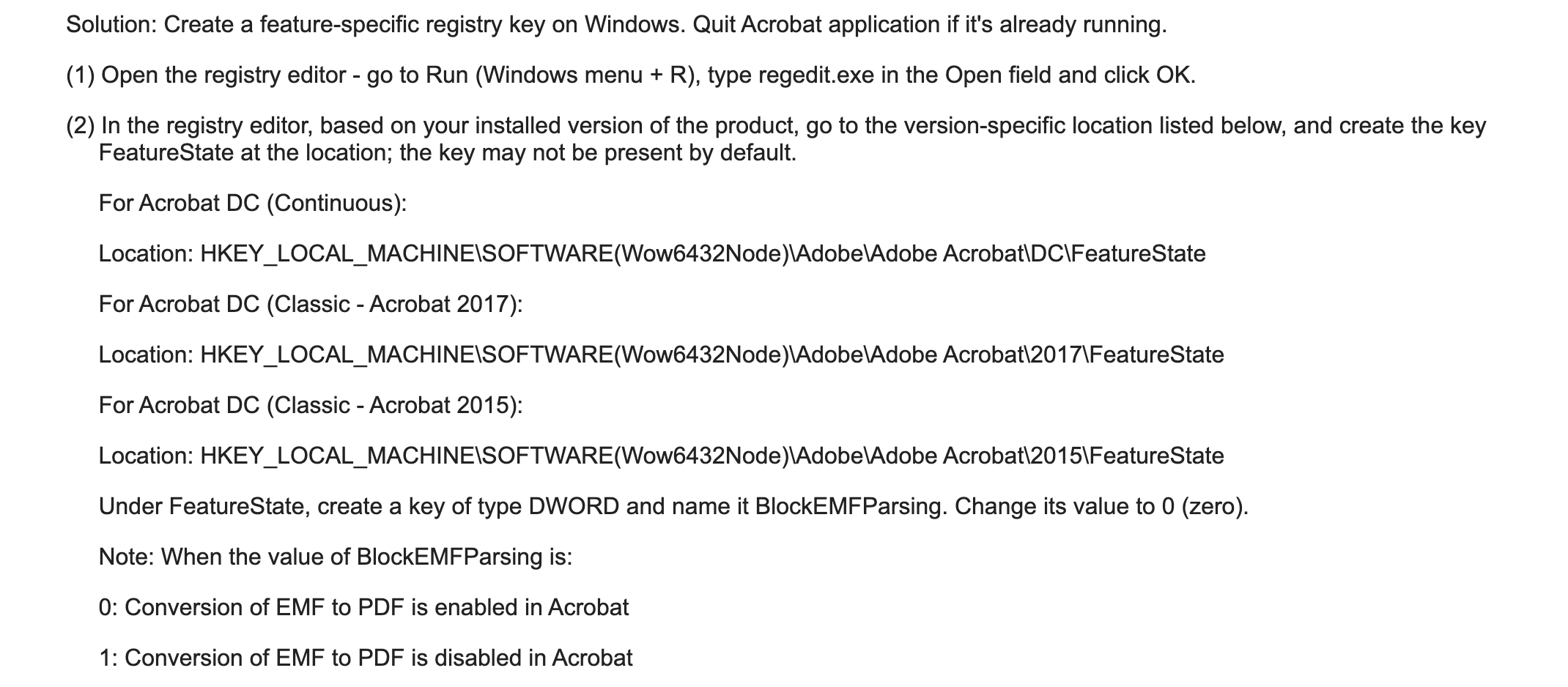
- Follow the following instructions to enable the feature of converting an EMF file to a PDF shown below:
- Open the EMF PoC in Adobe Acrobat
Case Studies
Case 1 - Heap Buffer Overflow
This bug can be triggered via opening a malformed EMF file in Adobe Acrobat, which causes a heap buffer overflow when Adobe Acrobat improperly processes Enhanced Metafile Format (EMF) data related to the handling of the EMR_COMMENT record. Figure 1 shows a comparison between a properly structured EMF file with a minimized PoC file that triggers this vulnerability.
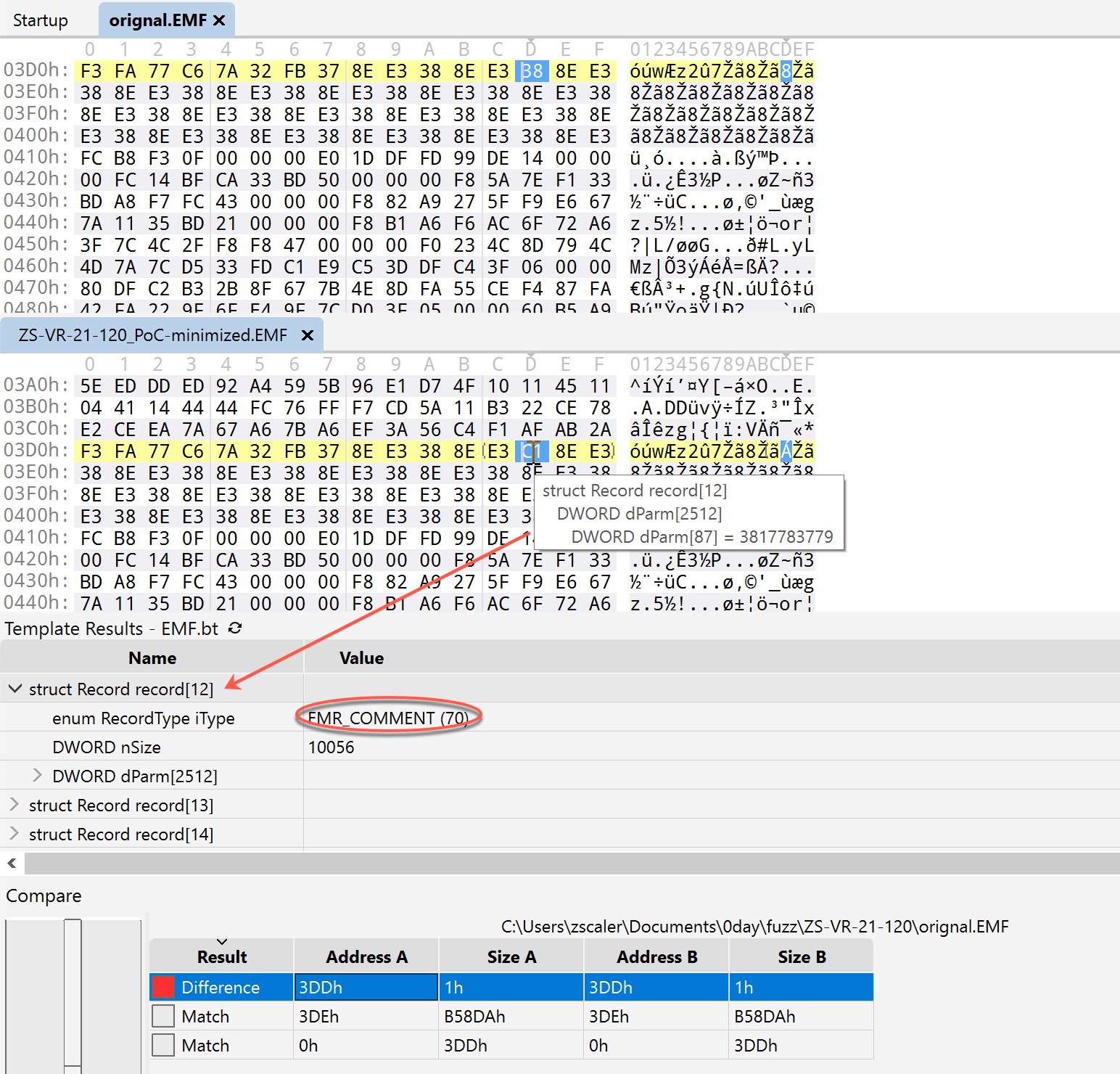
Figure 1. Comparison between a normal EMF file and the minimized PoC file that triggers a heap buffer overflow
Adobe Acrobat will produce the following crash shown in Figure 2.
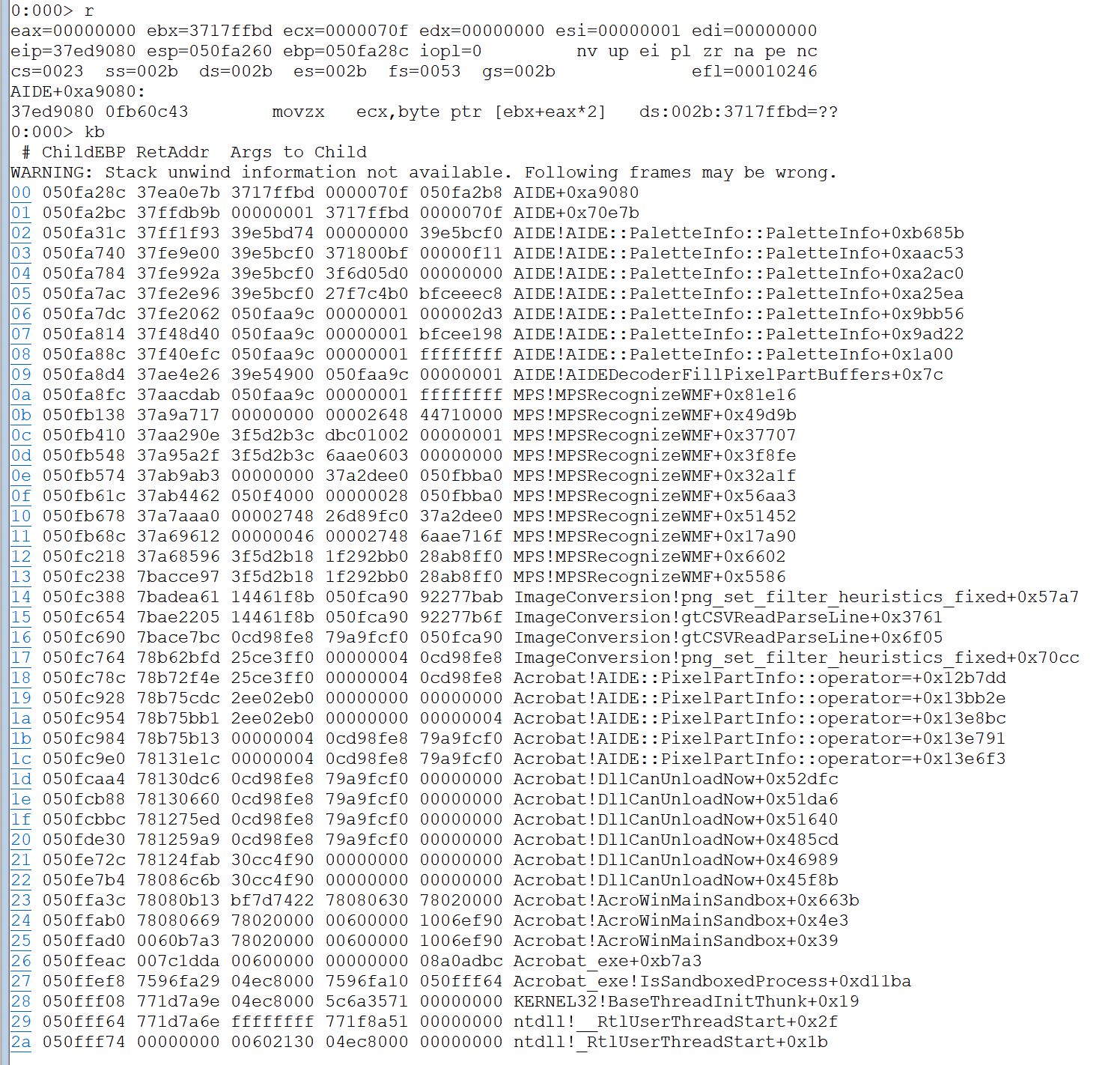
Figure 2. Adobe Acrobat EMF to PDF heap buffer overflow crash
Case 2: Use-After-Free
This bug can be triggered via opening a malformed EMF file in Adobe Acrobat, which causes a use-after-free crash when Adobe Acrobat improperly processes Enhanced Metafile Format (EMF) data related to the handling of the EMR_COMMENT record. Figure 3 shows a comparison between a properly structured EMF file with a minimized PoC file that triggers this vulnerability.
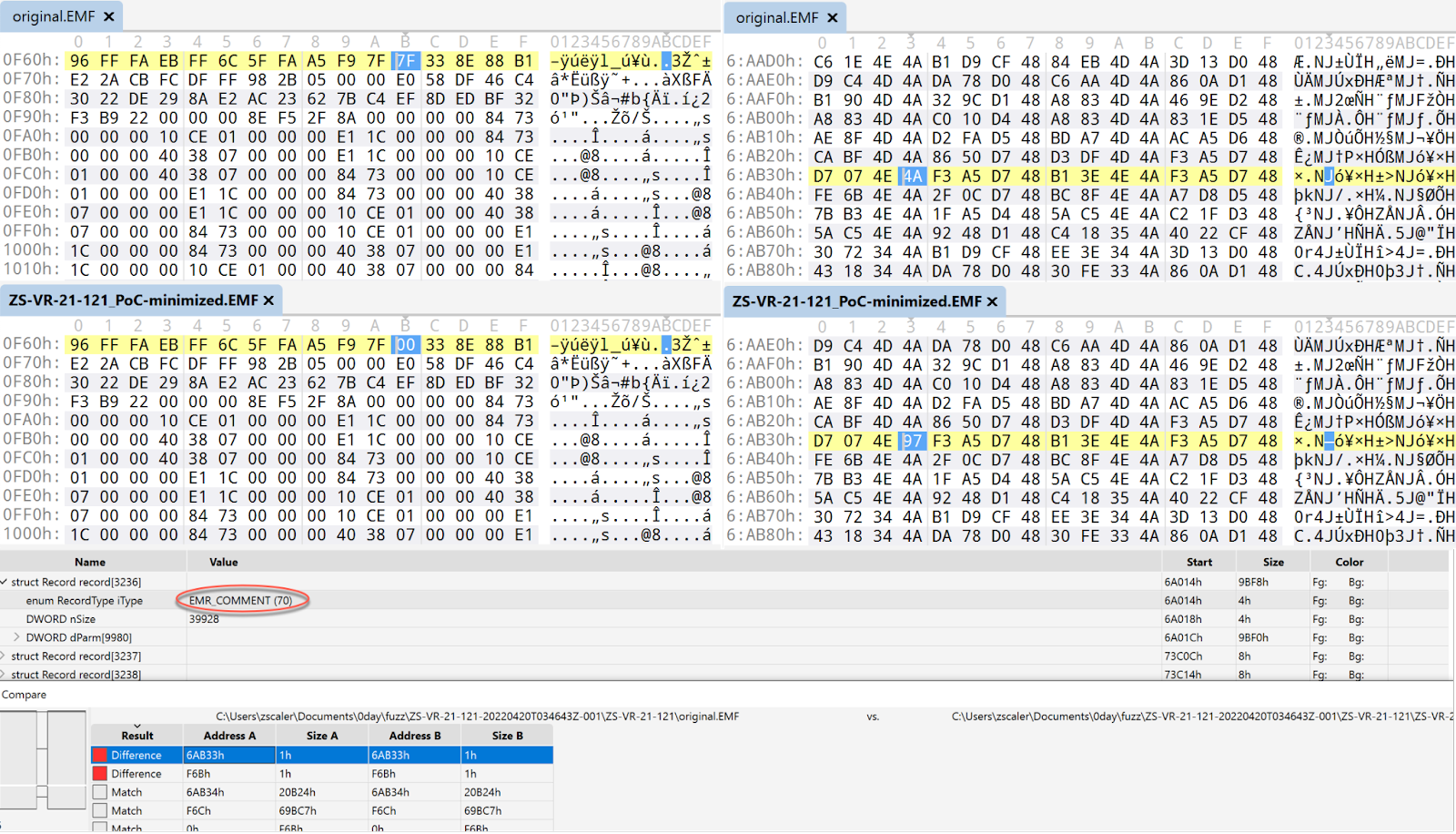
Figure 3. Comparison between a normal EMF file and the minimized PoC file that triggers a use-after-free crash
Adobe Acrobat will produce the following crash shown in Figure 4.
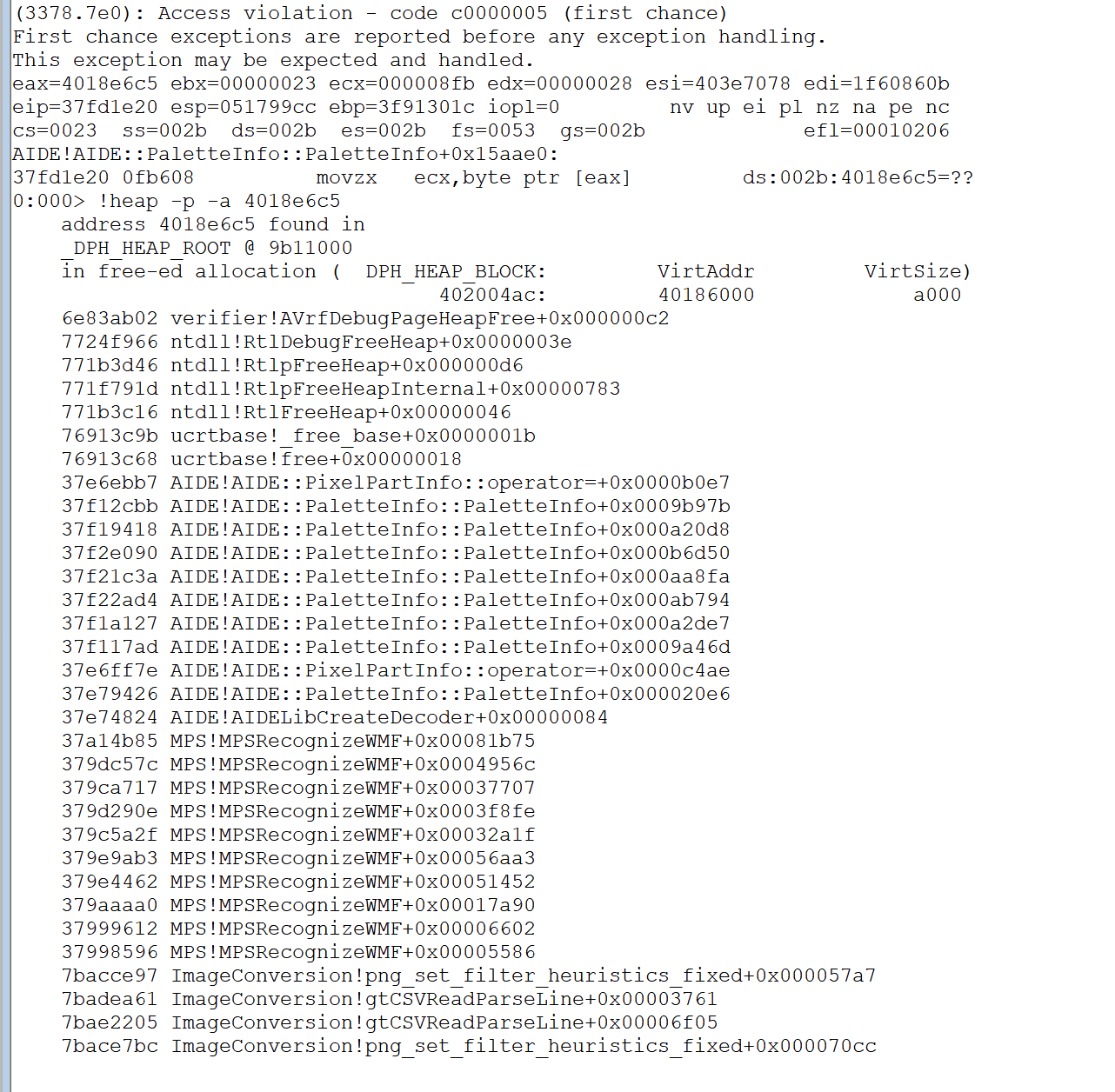
Figure 4. Adobe Acrobat EMF to PDF use-after-free crash
Case 3: Out-of-Bounds Read
This bug can be triggered via opening a malformed EMF file in Adobe Acrobat, which causes an out-of-bounds read when Adobe Acrobat improperly processes Enhanced Metafile Format (EMF) data related to the handling of the EMR_COMMENT record. Figure 5 shows a comparison between a properly structured EMF file with a minimized PoC file that triggers this vulnerability.
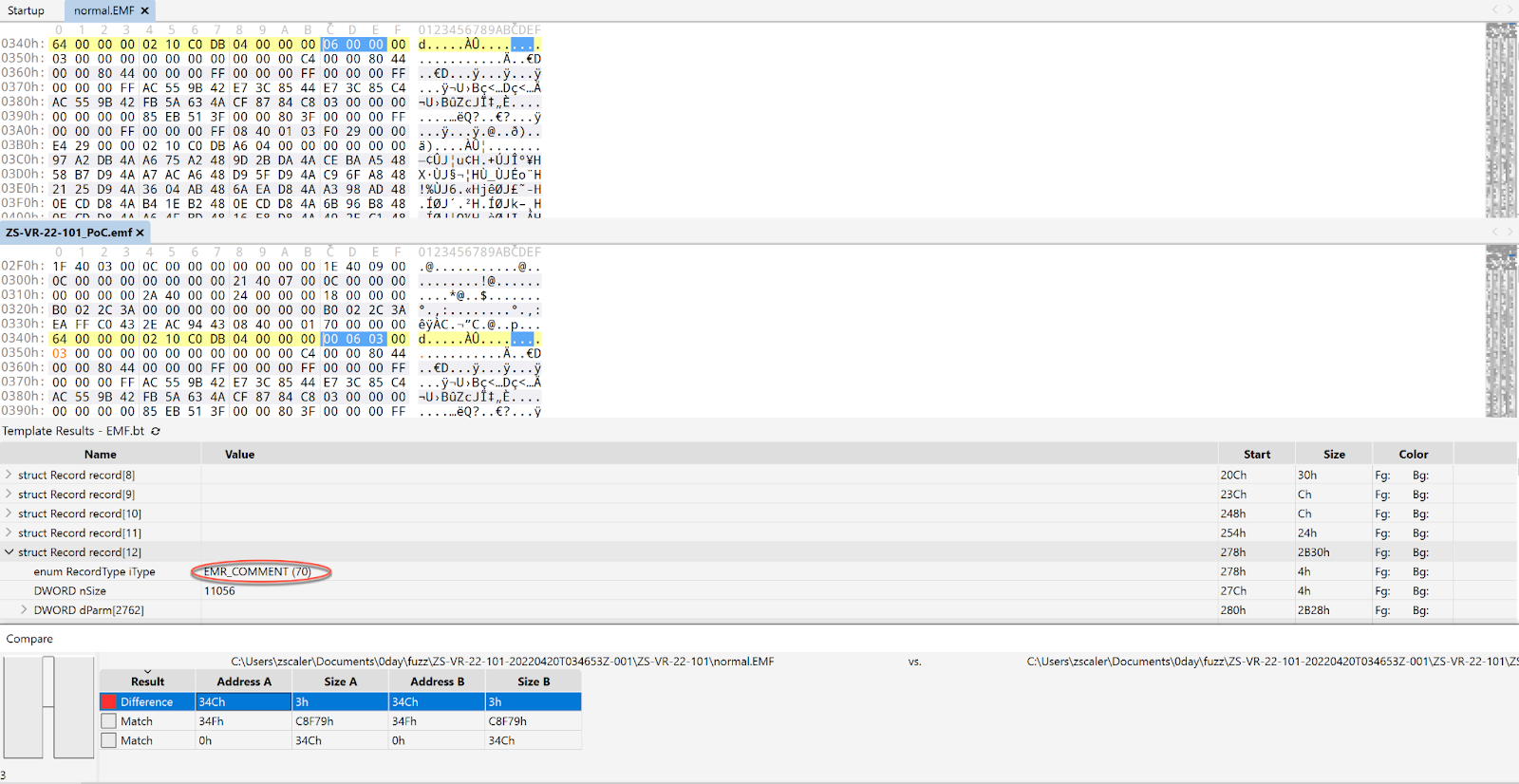
Figure 5. Comparison between a normal EMF file and the minimized PoC file that triggers out-of-bounds read
Adobe Acrobat will produce the following crash shown in Figure 6.
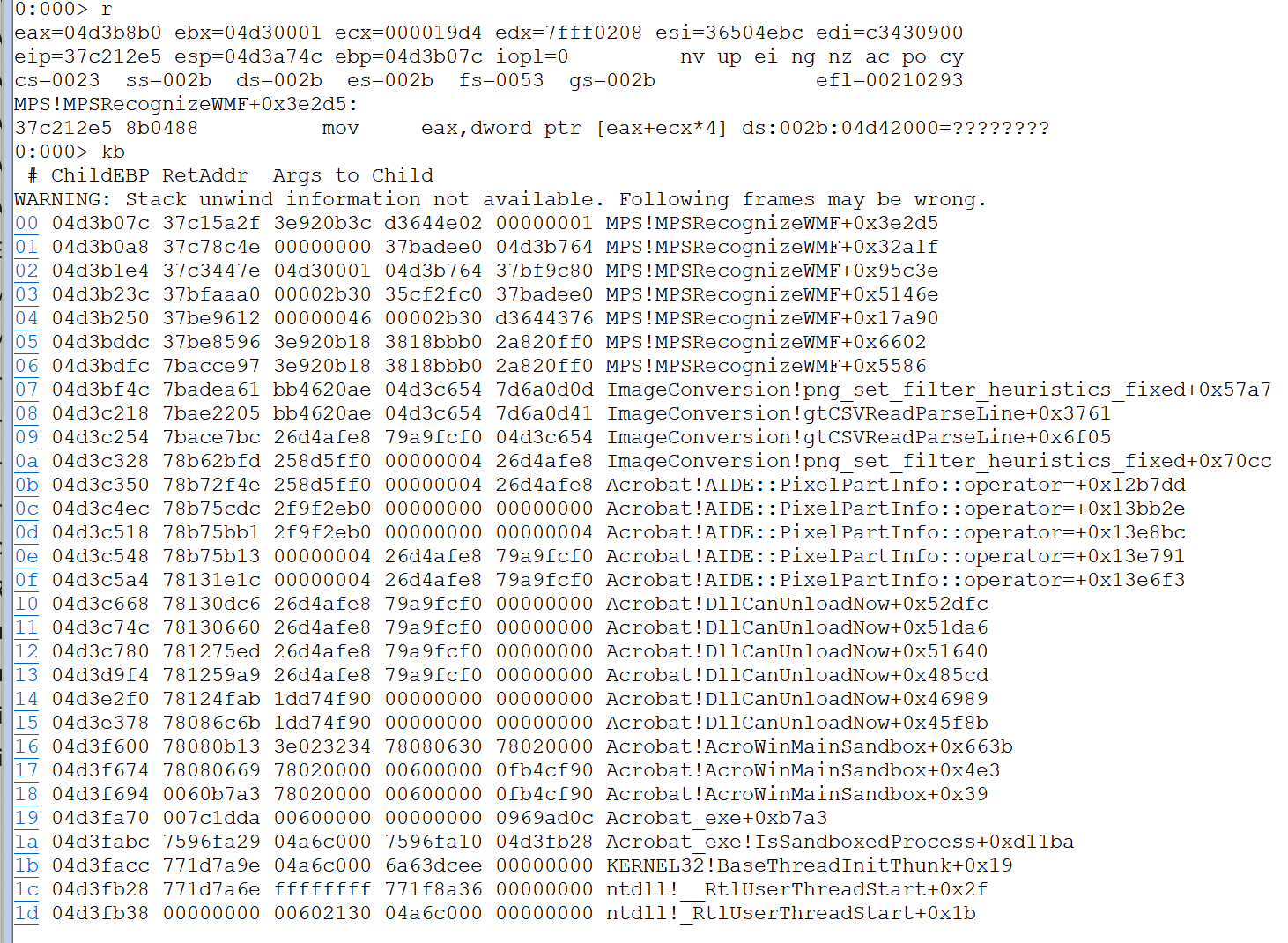
Figure 6. Adobe Acrobat EMF to PDF out-of-bounds read crash
Case 4: Heap Buffer Overflow
This bug can be triggered via opening a malformed EMF file in Adobe Acrobat, which causes a heap buffer overflow when Adobe Acrobat improperly processes Enhanced Metafile Format (EMF) data related to the handling of the EMR_COMMENT record. Figure 7 shows a comparison between a properly structured EMF file with a minimized PoC file that triggers this vulnerability.
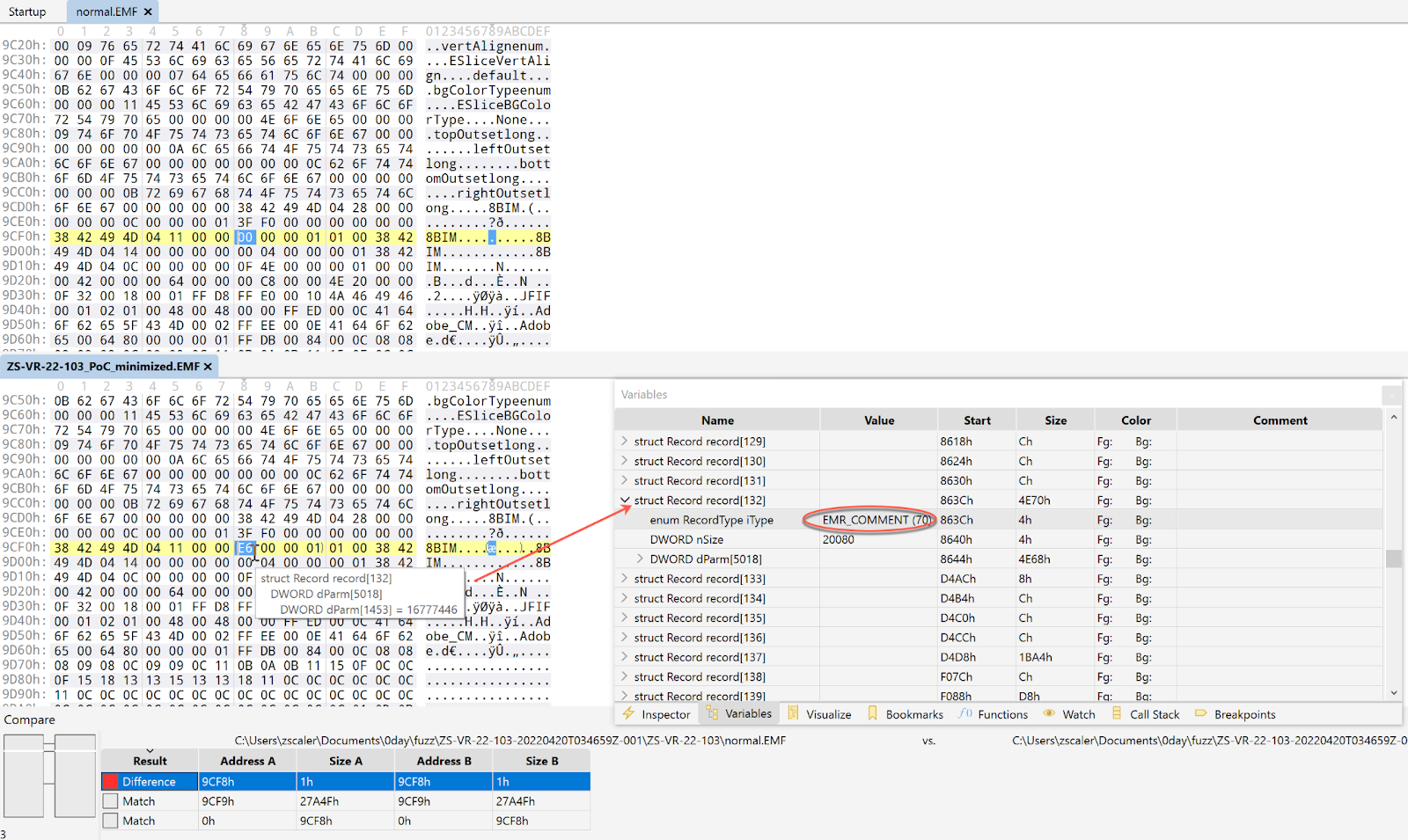
Figure 7. Comparison between a normal EMF file and the minimized PoC file that triggers a heap buffer overflow
Adobe Acrobat will produce the following crash shown in Figure 8.
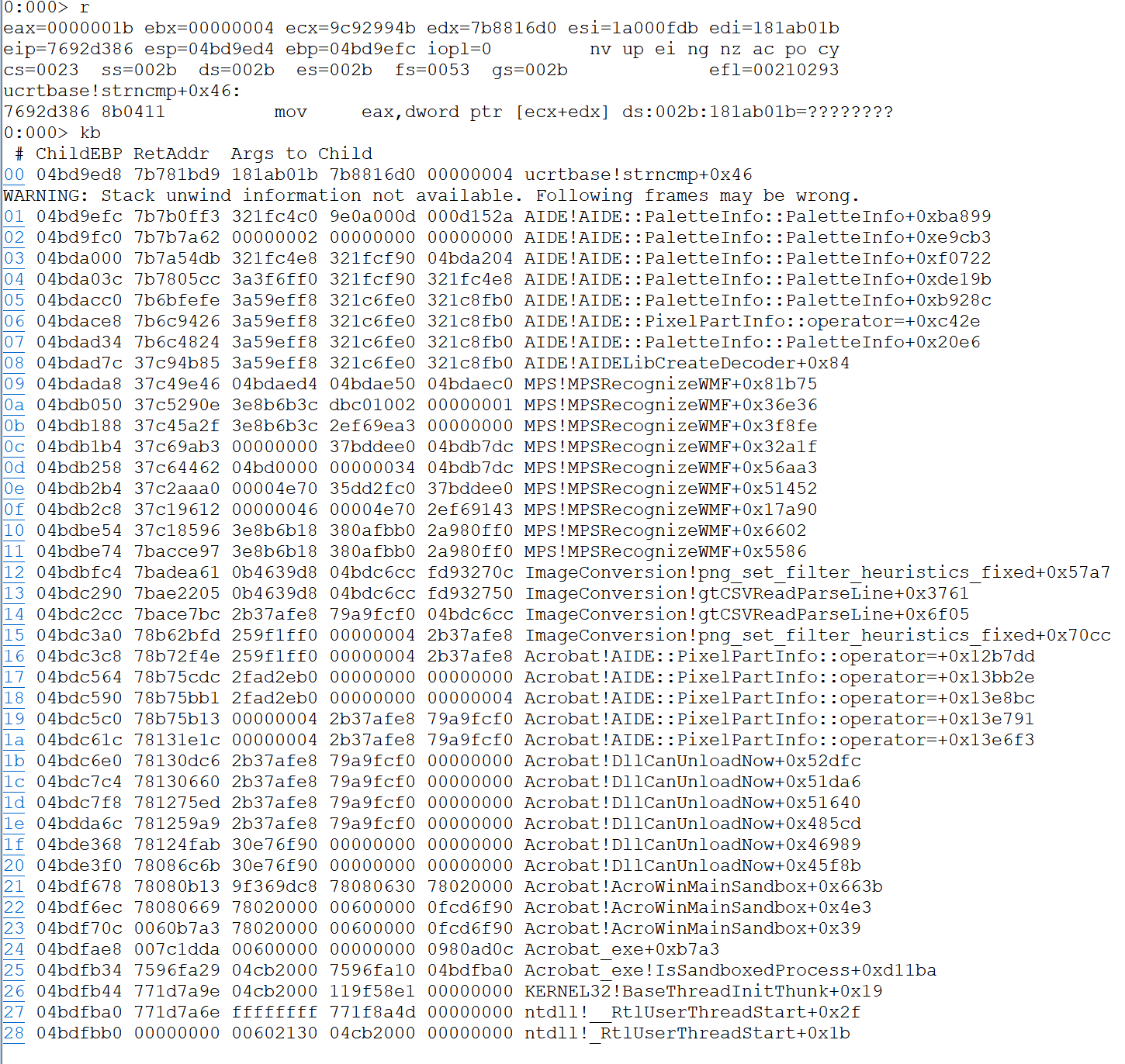
Figure 8. Adobe Acrobat EMF to PDF heap buffer overflow crash
Case 5: Null Pointer Dereference
This bug can be triggered via opening a malformed EMF file in Adobe Acrobat, to produce a null pointer dereference crash as shown in Figure 9.
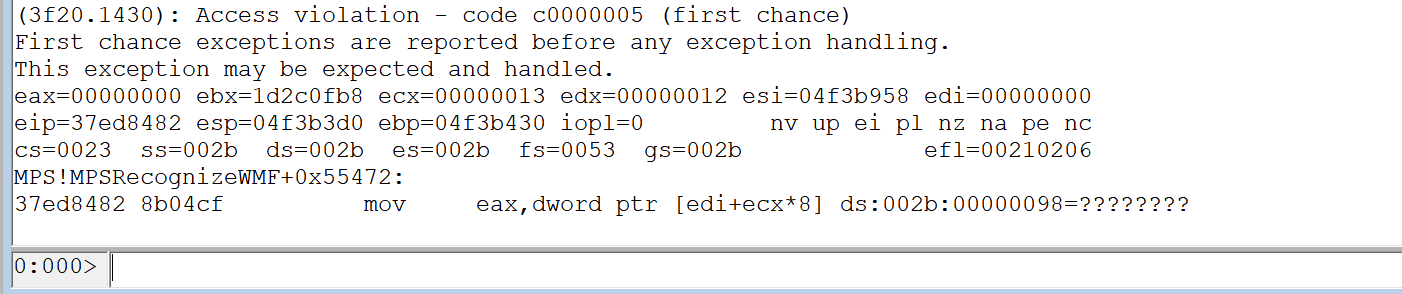
Figure 9. Adobe Acrobat EMF to PDF Null pointer dereference crash
Summary
In EMF records, the Comment record types define formats for specifying arbitrary private data, embedding records in other metafile formats, and adding new or special-purpose commands. Since an EMR_COMMENT record can contain arbitrary private data, ThreatLabz has found that it can be a potential attack vector. As presented in these case studies, four bugs were discovered by ThreatLabz in Adobe Acrobat when Adobe Acrobat improperly processes Enhanced Metafile Format (EMF) data related to the handling of the EMR_COMMENT record, in addition to a null pointer dereference.
Mitigation
All users of Adobe Acrobat and Reader are encouraged to upgrade to the latest version of the software. Zscaler’s Advanced Threat Protection and Advanced Cloud Sandbox can protect customers against these vulnerabilities.
PDF.Exploit.EMF2PDFMemoryCorruption
Reference
https://helpx.adobe.com/security/acknowledgements.html
https://helpx.adobe.com/security/products/acrobat/apsb22-16.html





